
If you’ve been following the news recently, you’ll know that cybersecurity is becoming increasingly important. It’s crucial that company executives take the threat of a cyber-attack seriously, as a data breach has the potential to inflict long-lasting, perhaps irreversible, damage on an organization. Fortunately, as you’ll see in our brand new comic story, Gemalto’s Cyber Investigator Chronicles, enterprises can protect themselves if they take the threat seriously. To defeat your enemy, you must understand their motives and techniques.
Here’s a guide to the villains of our Cyber Investigators comic. While they may be fictional, there are many, many people exactly like them across the world, ready to attack your organization. That’s why you must be prepared.
And don’t worry, before you ask, there aren’t any spoilers.
The hacktivists
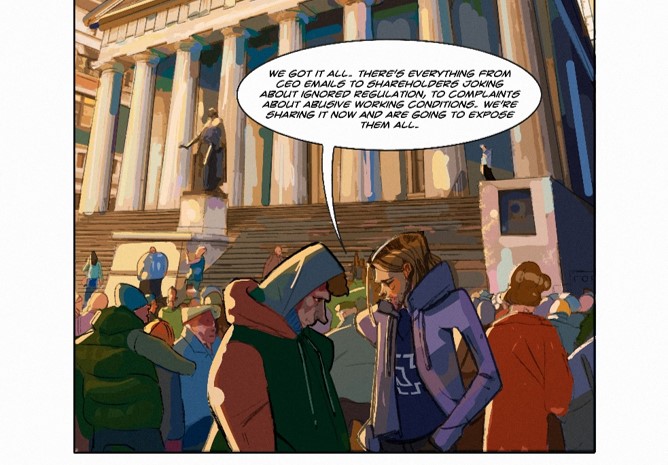 As you’ll find out in our comic, not all hackers are driven by money. Some seek to destabilize governments and organizations in pursuit of political ambitions. A recent example was the cyber-attack on the Democratic National Committee, which was probably politically motivated. Often these hackers seek to acquire emails or documents that could cause embarrassment for an organization or state institution. Alternatively, they might try to shut down a company’s networks, preventing the enterprise from functioning and inflicting long-term damage.
As you’ll find out in our comic, not all hackers are driven by money. Some seek to destabilize governments and organizations in pursuit of political ambitions. A recent example was the cyber-attack on the Democratic National Committee, which was probably politically motivated. Often these hackers seek to acquire emails or documents that could cause embarrassment for an organization or state institution. Alternatively, they might try to shut down a company’s networks, preventing the enterprise from functioning and inflicting long-term damage.
The mercenaries

A lot of hackers are just in it for the money. As our comic villain says, “we’re going to make a fortune”. Cyber-attackers who fall into this description use lots of devious techniques. Some use malware to exploit a vulnerability in security systems, accessing customer data, which they then sell on the dark web (if you’re unsure what we mean by ‘dark web’, check out our JustAskGemalto website). Others might block access to data on individual machines or servers, using malicious software called ransomware, and demand large sums of money to restore access. This type of attack has become increasingly common, affecting several hospitals in the United States.
The malicious insider

Sometimes hackers act in conjunction with a malicious insider at an organization or government body. These people can have different motivations – as we promised no spoilers, we won’t reveal anything here about our comic book villain’s intentions. These insiders might provide their username and password to a devious cyber-attacker, or deliberately leak confidential information to embarrass their employers, or give privileged access to an attacker through some other means.
There are other players in the cyber attacker landscape; anarchists after chaos and disorder, opportunists, egotists trying to demonstrate their cleverness and nation states or corporations engaging in (corporate) espionage.
As you can see, hackers can have a variety of motives, and can be extremely devious in achieving them. You may not think yourself a target, but if your customer is one, or you’re a supplier to another, you may fall into the crosshairs. By securing the breach, taking steps to deploy effective authentication, encryption and key management systems, it’s possible to reduce the impact of any cyber-attack.
To find out more about the different types of hackers – and, crucially, how to stop them – make sure you read our comic and follow the Cyber Investigators as they fight some dangerous enemies. Plus, you can join our CrowdChat, where our real life Cyber Investigator, Jason Hart, will be taking part in a discussion on issues raised in our story.


