This post originally appeared on SafeNet’s The Art of Data Protection blog prior to Gemalto’s acquisition of SafeNet.
Marty didn’t always have it easy. Growing up, he lived in poverty for much of his young life, doing odd jobs around his small town to provide for his family. His small town upbringing and family struggles taught him early on the importance of hard work, integrity, and to trust those around him. When he wasn’t working or going to school, he would spend hours reading classic literature and history. Marty, even with all of his troubles, was top of his class.
You can imagine how elated he and his family were for him to get a full college scholarship at an Ivy League school. Just like his childhood and teenage years, his college years were no different. He worked hard and graduated at the top of his class with a finance degree, and he was now heading up a major investment firm in New York.
Dedication, financial responsibility and good investments – both for himself and his clients – paid off. Thanks to a lifetime of saving and avoiding extravagance, by the time he reached the age of 28, Marty was nearly a millionaire. Marty liked his career because it was challenging, and it also gave him the chance to give back by helping people get the money they needed to give their families better lives. As a result, even with all of the riches, Marty didn’t lose his passion, work ethic, and optimism; he believed others would do the right thing when given the opportunity.
This made Marty a great boss and friend. It’s also what made him a target. Unfortunately, trusting others as much as he did, Marty didn’t worry much about identity protection.
The one real indulgence Marty had was getting the latest and greatest tech devices. When he showed up to the office with a new smart watch one day, “Malevolent” Marie, his assistant, saw the opportunity she’d been looking for.
There was a large gap in her resume after college. While she’d told Marty that this was time spent traveling across Europe during her job interview a few months ago, in reality, it had been time spent hacking. She’d tried doing a 9-5 and operating within the limits of the law, but that grew tiresome. Now, she was ready to put her hacking skills to use one more time and retire for good.
Marty’s work computer was far too secure for her liking thanks to IT, and he never connected his personal phone to the office Wifi because it could be spotty. But this new device could change things.
She did a little research online, and was ready the next day. Marie complemented Marty on the new watch, and asked if he was seeing a drop in his phone’s battery life as a result of connecting to the watch constantly — something her research said was a common complaint.
When Marty confirmed a decline in his battery life was the one downside to the watch, she casually recommended that he start connecting to the Wifi to offset the new demand on the battery a bit, adding for good measure that the network was performing much better for her these days.
She didn’t have to wait long. Within half an hour, Marty was connected to the Wifi with his phone and watch. She knew this for a fact thanks to her karma attack.
When Marty had headed back to his office after their conversation, she’d set up a rogue hotspot and configured it to pose as the office Wifi. When Marty connected to the network, he was really connecting to Marie’s hotspot, and it gave her the starting point she needed to get the information she was after. After that, all she had to do was wait until Marty went online and logged into a few accounts. Hours later, she’d managed to capture and decrypt his passwords for his email, Facebook, and — the motherload — his bank accounts.
As expected, she found Marty used the same email address and password for just about everything — including his online log-ins for his banking accounts — and he hadn’t bothered taking advantage of the other authentication options the sites offered.
She worked quickly to transfer funds from Marty’s accounts to an off-shore account she’d set-up. For good measure, she also changed the passwords to Marty’s bank and email accounts, just in case any alerts were attempted.
Unfortunately for Marty, who had worked hard to build his nest egg, Marie now had her retirement plan set.
The following day, he was shocked when he didn’t see Marie at her desk when he got in, but assumed she’d just hit some traffic. Instead, she was on a plane headed for the Caribbean. It was a one way ticket.
By the time Marty put together all of the pieces, it was too late. “Malevolent” Marie was already gone with his life savings… and his nightmare had just begun.
 In the above scenario, Marty would have to go through legal channels to attempt to locate Marie, seize the account funds, and bring her back from the Caribbean for justice. One could only imagine Marty’s dismay when he first realized what had happened, but how could this nightmare be avoided?
In the above scenario, Marty would have to go through legal channels to attempt to locate Marie, seize the account funds, and bring her back from the Caribbean for justice. One could only imagine Marty’s dismay when he first realized what had happened, but how could this nightmare be avoided?
A critical security misstep here was Marty’s lack of two-factor authentication for his mobile banking application. Too many individuals rely on username and password for account access, and often times, they write-down those same passwords on paper or save them in documents they believe are safeguarded.
Had Marty signed-up for the two-factor authentication option offered by his bank, Marie would have needed to not only locate his username credential, but also obtained Marty’s token for the next layer of account access protection.
To find out more about how two-factor authentication can help you, visit our Online Banking Security page.
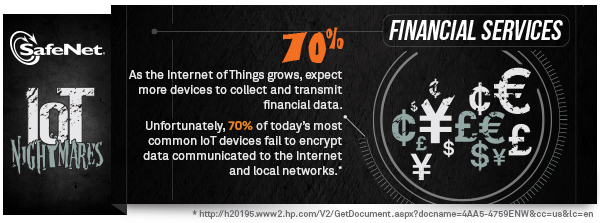
The IoT Nightmares don’t end here!
Check out the previous entries in the IoT Nightmares series — Who Turned Out the Lights? and Prison Break.