Mobile devices play a leading role in all of our lives – with smartphone penetration reaching 75% in the US just a few days ago. And with news of high-profile companies such as Sony Pictures and a-list celebrities getting hacked hitting the headlines on a regular basis, it’s no wonder mobile security is getting higher on the agenda.
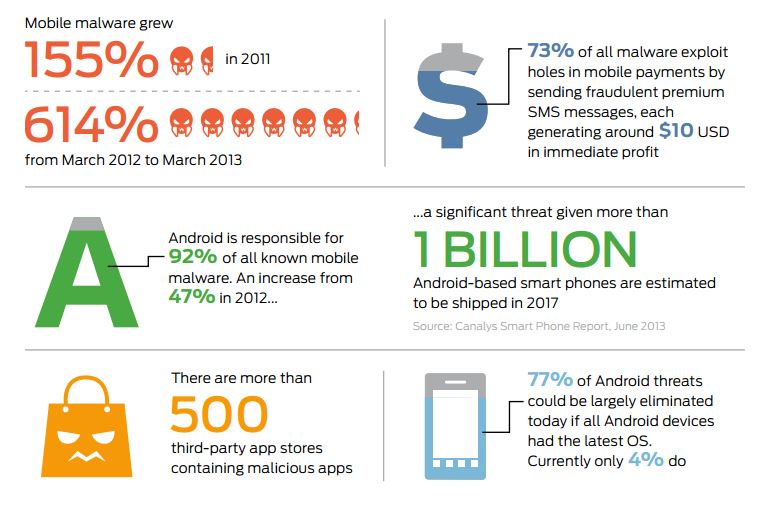
As this infographic shows, the threat to end-users using mobile devices to access services and the companies which provide them is huge.
In response to this, yesterday we extended the reach of our Allynis Trusted Services Hub to over an additional 350 million mobile devices equipped with Trustonic Trusted Execution Environment (TEE).
A TEE is a secure area that resides in the application processor of an electronic device. To help visualize, think of a TEE as somewhat like a bank vault. A strong door protects the vault itself (hardware isolation) and within the vault, safety deposit boxes with individual locks and keys (software and cryptographic isolation) provide further protection. You can read more about the TEE here.
From a Bank or service provider’s perspective, using this security framework means that they can address potentially more than 350 million end users who are equipped with TEE-capable devices. This includes Samsung Galaxy range and other mobile devices from major handset makers.
In addition to this, TEE is mobile device agnostic and not tied to a specific phone brand. The new secure platform also use cases agnostic, which means easy service deployment for service providers.
Since this platform has access to multiple resources on the device, this opens the door to many different possibilities for service providers that want to secure many different services on mobile devices, making the most of the resources on the phone itself.
You can find out more about how to facilitate your secure service deployment via TEE with the Gemalto Trusted Service Hub here.