This post originally appeared on SafeNet’s The Art of Data Protection blog prior to Gemalto’s acquisition of SafeNet.
Our new prisoner had been here only a few days, but he was already causing a stir among his fellow inmates. Thrown in with two-bit crooks, robbers, rapists, and murders, we all chuckled at the sight of him. Mid-twenties, slight, and no taller than 5’ 8”, Mark Davis looked wildly out of place among the inmate population at Jefferson Penitentiary. His dossier told another story. Part of a team of hackers accused of perpetrating some of the most prolific breaches the world had ever seen, for years he was known simply as De1!ingr.
His luck ran out. Convicted of 10 counts of Computer Misuse, De1!ingr found himself confined to a 6×8’ jail cell, and deprived of any contact with a computer whatsoever. And yet, he seemed at ease.
The other guards and I watched as he mingled—no—held court, with other inmates. They listened intently as he spoke, as if everything he said were the gospel.
“He’s getting along nicely,” the other guards would say sarcastically.
We were dumfounded. That is, until Sunday evening.
***
In the early hours of Monday morning I was awakened by the sound of a ringing telephone. It took the panicked voice on the other end several attempts to slow down and explain the situation: our resident hacker had escaped.
The security cameras told the story. Prisoners, normally relaxed, appeared to be more awake than normal. They stirred in their cells as if they knew what was to come. Something was on their schedules that wasn’t on ours.
Then, it happened. In an instant each of the cell doors slid open.
Then the doors to the cell block slid open… and finally the doors leading out to the yard.
The guards on duty were stunned, and admittedly slow to react. By the time they had donned their riot gear, the prisoners were running through all corners of the prison. Chaos followed, as outnumbered guards in riot gear fought to subdue the prisoners.
It took several hours before the guards were able to regain control of the prison, and return the prisoners to their cells.
A head count revealed only one prisoner to be missing. In the confusion, De1!ingr had slipped away from the other prisoners, and fled through an open gate to an awaiting getaway car.
An investigation revealed that our systems had been hacked from the outside, undoubtedly by De1!ingr’s partners in crime. He was gone, and our no-escapes record shattered.
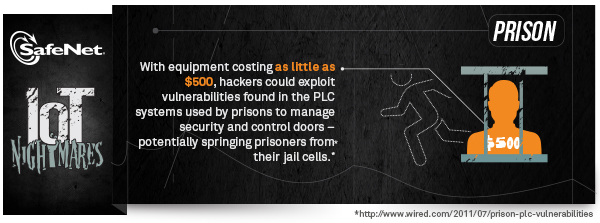
 While the story above may seem improbable, research into the vulnerability of correctional facilities revealed that prison cells can indeed be opened by compromising Programing Logic Controllers (PLCs). PLCs are small computers at the heart of keyless correctional facilities. They can be programmed to control a wide variety of things in a correctional facility including security cameras, to temperature controls, and cell doors.
While the story above may seem improbable, research into the vulnerability of correctional facilities revealed that prison cells can indeed be opened by compromising Programing Logic Controllers (PLCs). PLCs are small computers at the heart of keyless correctional facilities. They can be programmed to control a wide variety of things in a correctional facility including security cameras, to temperature controls, and cell doors.
Organizations have only recently become aware of the vulnerability of PLC systems, in large part due to the Stuxnet breach. Stuxnet was one of the first attacks designed to target PLCs with the goal of compromising nuclear centrifuges, and it did so by signing malware with a private key, stolen from a certificate authority, to make it appear as trusted code. Over time this code worked its way to the PLC system, and wreaked havoc. Using a similar approach researchers have managed to compromise the systems of correctional facilities, and manipulate the cell doors.
Certificate Authorities, form the root of trust for the systems we depend on every day. When private keys and certificates are compromised the systems built on that trust fall apart. Preventing attacks of this type requires robust security for the private keys and certificates to ensure only legitimate code is signed. Hardware Security Modules (HSMs) are designed for this purpose, and are the best way to protect cryptographic keys and certificates.
For more information, visit our HSMs for Code Signing page.
The IoT Nightmares don’t end here!
Check out the previous entry in this series, IoT Nightmares: Who Turned Out the Lights?


