You may not know it, but 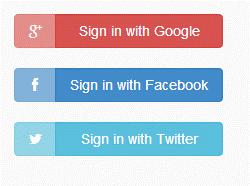 chances are that you already use an identity provider, or two, in your everyday consumer life. When you log in to a new retail website by clicking “Sign in with Google” or “Sign in with Facebook,” that’s an example of Google or Facebook acting as a trusted identity provider (IdP), and authenticating you on behalf of that online store.
chances are that you already use an identity provider, or two, in your everyday consumer life. When you log in to a new retail website by clicking “Sign in with Google” or “Sign in with Facebook,” that’s an example of Google or Facebook acting as a trusted identity provider (IdP), and authenticating you on behalf of that online store.
By entering your username, password and sometimes a 2nd authentication factor, Google or Facebook can assert whether you are who you claim to be, and relay their authentication decision to the retail or media site in question.
Essentially, an Identity Provider is a trusted system that authenticates users for the benefit of other, unaffiliated websites or digital resources.

The beauty of using an identity provider is that it:
- Saves you, the end-user, the pain of creating and maintaining a new password.
- Spares your favorite retail or media websites the trouble of storing and protecting that information. In fact, since the authentication process is relayed to Google, the retail website never sees your password or other authentication credentials.
In enterprise settings, the list goes on:
- Compliance is easier to maintain since the IdP provides a central audit trail of all access events, making it easy to prove that you know who is accessing what and when (critical for mandates such as PCI DSS, GDPR)
- Help desk costs associated with password resets are eliminated, estimated at 20% of all support tickets according to a recent Gemalto survey.
Amateur vs. Pro – The Advantages of a Specialized Identity Provider
Considering the breaches of myriad of service providers’ user credential databases (read Yahoo, LinkedIn and Bitly breaches of yesteryear) and the resulting leak of passwords stored in plaintext or using weak hashing algorithms, a specialized identity provider offers another advantage: The ability to add additional layers of protection to safeguard your identity against phishing, simple malware, brute-force attacks and credential database breaches. Such layers include strong multi-factor and context-based authentication, as well as strong encryption.
How Federated Authentication Works
So how does federated authentication work, meaning the process of authenticating using a trusted IdP? The answer is quite simple:
- Each time a user attempts to log in to a website or cloud app, they are redirected to a trusted identity provider that has been preconfigured to accept authentication requests from that unaffiliated website or cloud application.
- The IdP collects the user’s credentials, for example, their username and one-time passcode (OTP) and returns an accept or reject, according to which a user is granted or denied access to the application.
NIST Guidelines and Adoption
The proliferation of digital identities and the need for federated authentication and cloud single sign on (cloud SSO) is well established, with 39% of organizations already using cloud SSO today. It comes as no surprise then that both SSO and federated authentication are listed as recommended controls in NIST’s latest draft of Security and Privacy Controls for Information Systems and Organizations (Special Publication 800-53r5) which is open for public commentary through September 15, 2017. For IAM professionals looking for state-of-the-practice guidelines, a dedicated Digital Identity Guidelines report (Special Publication 800-63-3) was released by NIST this last June, with its third part exclusively dedicated to Federated Authentication.
Ready to learn more about identity providers and federated authentication? Get started by downloading the Access Management Handbook, or watch the webinar “What is An Identity Provider and Do You Need One?”


